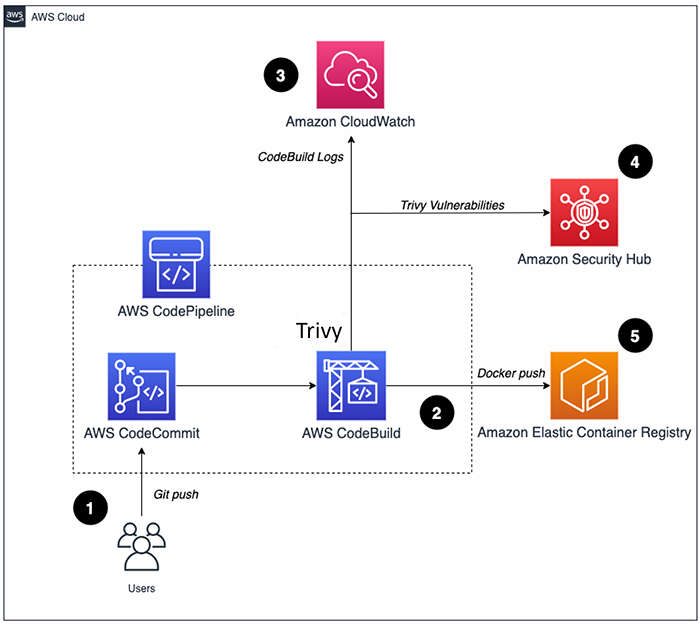
How to build a CI/CD pipeline for container vulnerability scanning with Trivy and AWS Security Hub | AWS Security Blog

Fingerprint Scanner on Wall for Unlock Door Security System Editorial Stock Image - Image of button, identity: 128469239

Products Archives | SAP Vulnerability Assessment | SAP Security Monitoring | SAP Security Scan | SAP SIEM Integration | SAP Pentesting | by ESNC GmbH